The Truth About SSD TRIM: Why Your Deleted Files Aren't Actually Erased
Introduction
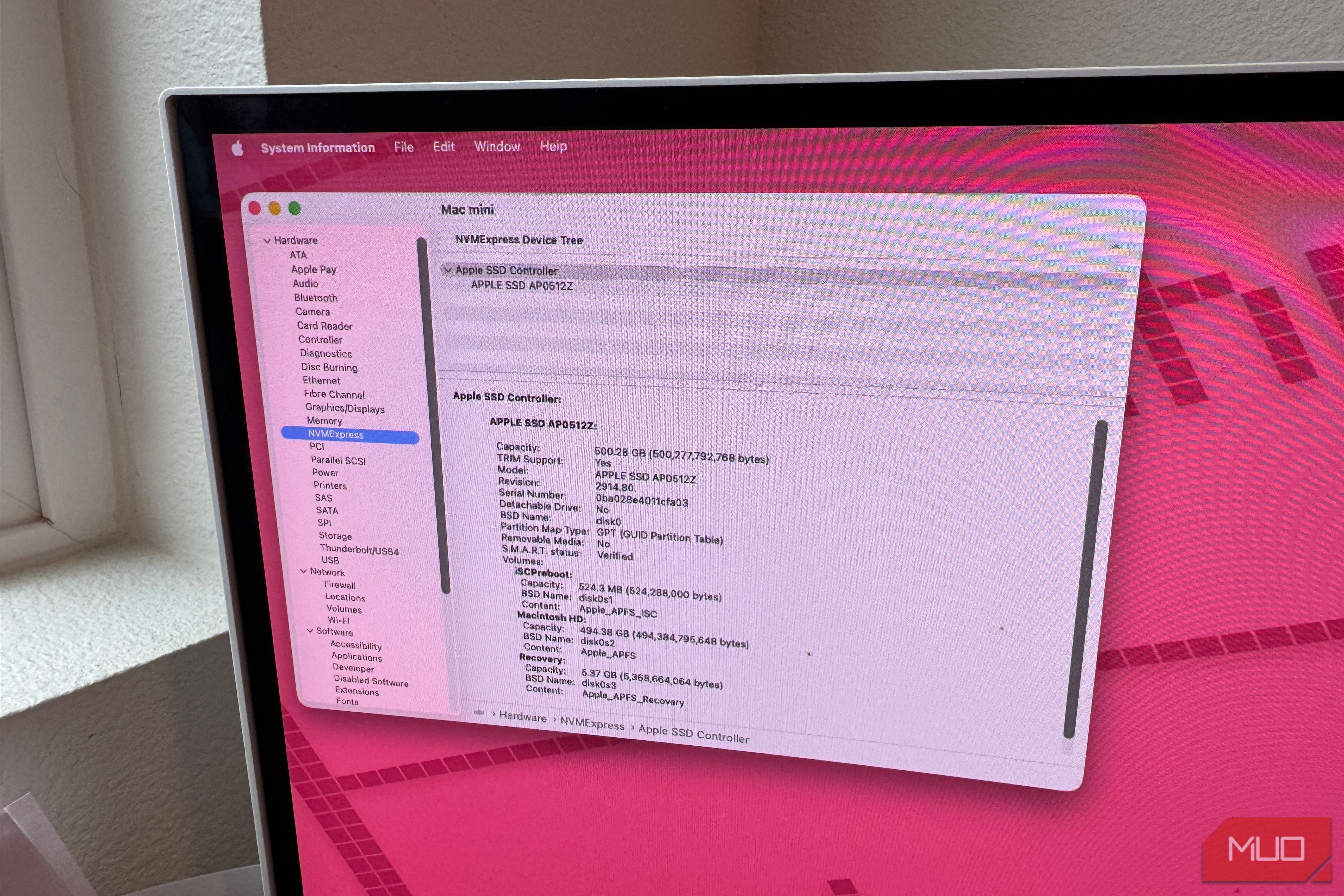
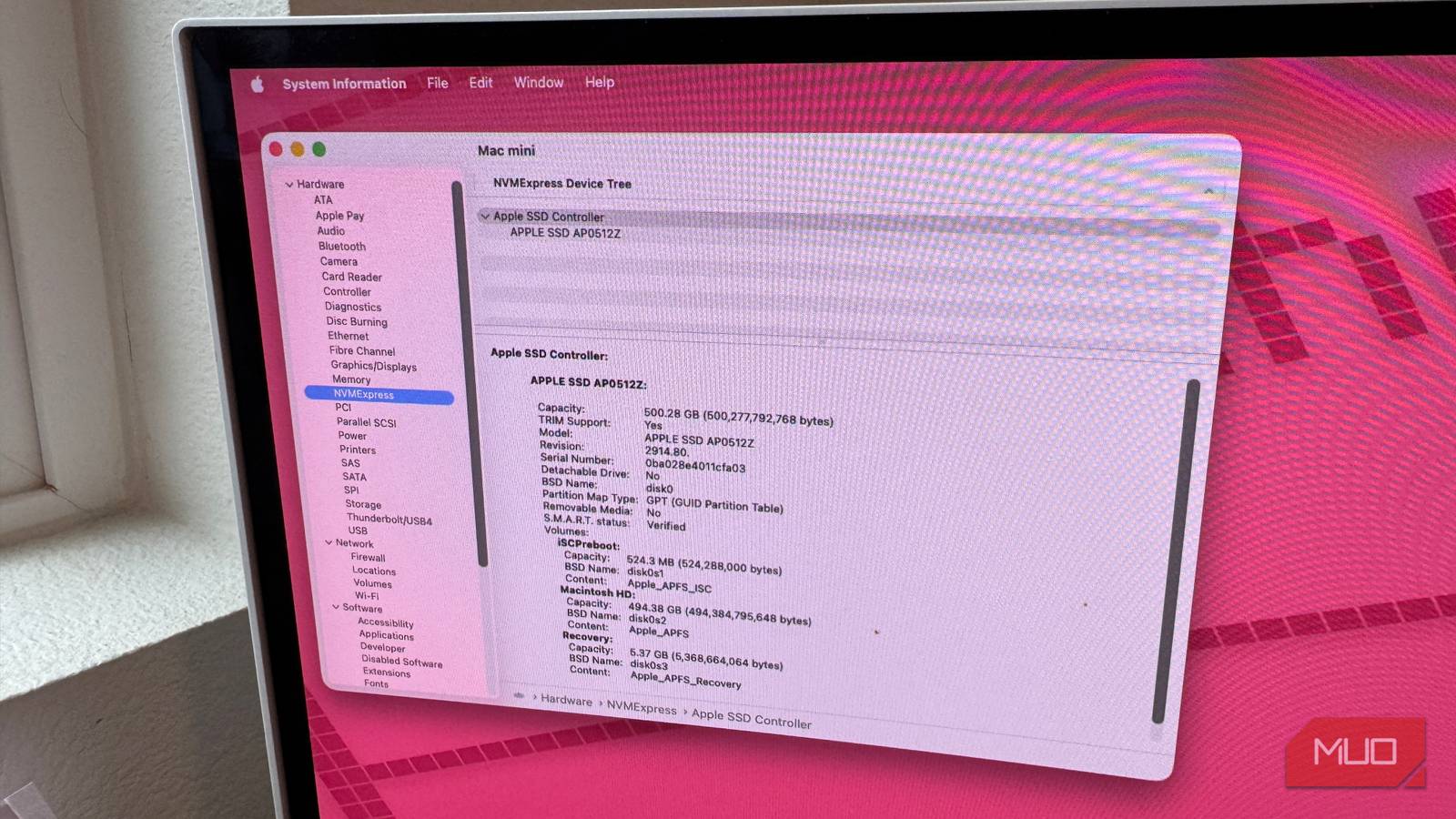
If you own a modern solid-state drive (SSD), you've probably heard of TRIM — a command that helps maintain your drive's performance. A common belief is that TRIM automatically wipes deleted files, protecting your privacy. While TRIM does mark data as invalid, it's not designed for secure deletion. Instead, its primary purpose is to keep your SSD fast. Understanding this distinction is essential for anyone who handles sensitive information.
What Is TRIM?
TRIM is an ATA command that tells the SSD controller which data blocks are no longer in use by the file system. When you delete a file on an SSD, the operating system doesn't immediately erase the data — it simply marks the space as available. Without TRIM, the SSD wouldn't know that those blocks are free, leading to slower write speeds over time as the drive has to erase old data before writing new data.
How TRIM Works
The internal workings of an SSD are different from a traditional hard drive. Data is stored in pages, grouped into blocks. Writing requires erasing an entire block, which is resource-intensive. TRIM allows the drive to perform garbage collection in the background — it consolidates valid data and erases unused blocks preemptively.
- On file deletion: The OS sends a TRIM command listing the logical addresses of the deleted file.
- Drive response: The SSD controller marks those pages as invalid.
- During idle time: The drive erases the invalid blocks, making them available for quick writes.
This process improves write performance significantly, but it does not guarantee that the original data is immediately overwritten or destroyed.
The Privacy Gap: Why TRIM Doesn't Erase Your Data
The misconception arises because people assume that once TRIM has processed a deleted file, the data is gone. In reality, the data remains physically in the NAND flash cells until those cells are actually overwritten by new data. This can happen at any time — minutes, hours, or even days after deletion, depending on the drive's workload and garbage collection schedule.
Data Recovery Risks
Because the data persists, it can be recovered using forensic tools or specialized hardware. This is a critical issue for:
- Sensitive documents — financial records, personal identification.
- Confidential business data — trade secrets, client lists.
- Previously encrypted files — if the encryption key is weak or lost, remnants may be recoverable.
Moreover, some operating systems or configurations may not send TRIM commands for external SSDs or certain file systems, leaving data even more vulnerable.
In short, TRIM is a performance feature, not a security feature. It does not actively sanitize your data.
How to Securely Erase Data from an SSD
For true peace of mind, you need to use methods specifically designed for data destruction. Here are the recommended approaches:
1. ATA Secure Erase
Most SSDs support the ATA Secure Erase command, which instructs the drive to internally wipe all user data at the hardware level. This typically renders data unrecoverable. Tools like hdparm on Linux or Parted Magic can invoke this command.
2. Full-Disk Encryption from the Start
If you enable encryption (see best practices below) before storing sensitive data, deleting the encryption key effectively locks the data away. Tools like BitLocker (Windows), FileVault (macOS), or LUKS (Linux) are excellent.
3. Overwriting (With Caution)
For HDDs, overwriting all sectors multiple times is effective. On SSDs, it's trickier because wear leveling may prevent overwriting all physical cells. However, a single pass of the entire drive (using a tool like dd with /dev/urandom) can be sufficient for modern SSDs.
- Note: Never rely solely on file-shredder apps that try to overwrite specific files, as SSDs may redirect writes.
Best Practices for Protecting Privacy on SSDs
To avoid relying on TRIM for security, follow these habits:
Encrypt Everything Ahead of Time
Enable full-disk encryption as soon as you set up your system. This ensures that even if data lingers after deletion, it's scrambled without the key.
Use Secure Deletion Tools for Specific Files
If you need to delete individual sensitive items, use tools that send the ATA Secure Erase for those logical blocks, such as srm (secure remove) configured for SSDs, or the secure-delete utility.
Be Cautious with External Drives
Not all external SSDs support TRIM over USB. Check your drive's specifications. If TRIM is not active, deleted files remain fully recoverable.
Regularly Perform Secure Erase Before Discarding
When selling or recycling an SSD, always run a full ATA Secure Erase (or encryption key purge) to prevent data leaks.
Conclusion
TRIM is a valuable technology for maintaining SSD performance, but it's not a privacy tool. The idea that your deleted files are automatically and securely wiped is a myth. By understanding the true role of TRIM and adopting proper data hygiene — especially encryption and hardware-level erasure — you can safeguard your information effectively. Don't assume your SSD is protecting your secrets; take control with the right methods.